What are Elementary Data Link Layer Protocols
Introduction
When the data link layer receives a packet, it is encapsulated in a frame, including a data link header and trailer. A frame is made up of an embedded packet that carries control information as well as a checksum. The hardware computes the checksum when a frame arrives at the receiver. If an error is discovered, it is reported to the data link layer. If no errors are detected, it simply checks the control data in the header and sends the packet to the network's layer.
Primary data link layer protocol Classification
Elementary Data Link protocols are divided into three types, as shown below-
- Protocol 1 − Unrestricted simplex protocol
- Protocol 2 − Simplex stop-and-wait protocol
- Protocol 3 − Simplex protocol for noisy channels.
Let us go over each protocol individually.
1. Unrestricted simplex protocol:
Data transmission is only done in one direction. Transmission (Tx) and reception (Rx) are always available; processing time is irrelevant. This protocol has an infinite buffer space and no faults, meaning no damaged or lost frames.
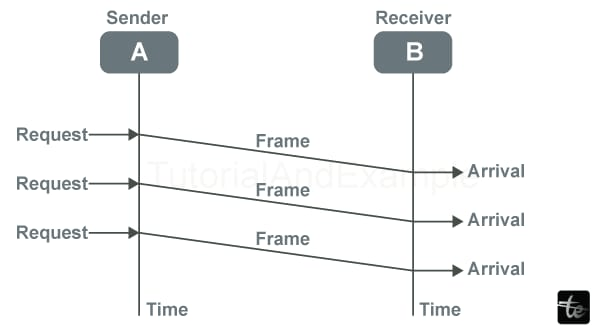
The graphic below depicts the Unrestricted Simplex Protocol-
2. Simplex stop-and-wait protocol:
This protocol assumes that data is only transferred in one way. There is no inaccuracy; the receiver can only process data constantly. These assumptions imply that the transmitter cannot send frames faster than the receiver can process them. The critical issue here is preventing the transmitter from flooding the receiver. The typical solution for this problem is for the receiver to provide feedback to the sender; the approach is as follows:
Step 1: The acknowledgement frame is returned to the sender, informing it that the most recently received frame has been processed and transmitted to the host.
Step 2: Permission is granted to send the following frame.
Step 3: The sender must wait for an acknowledgement frame from the receiver after transmitting the sent frame preceding sending another frame.
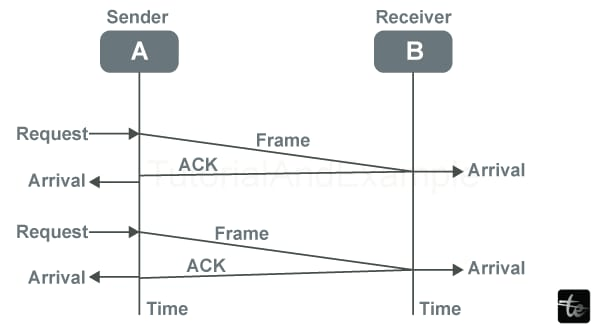
The Simplex stop-and-wait protocol is utilized when the sender sends one frame and waits for the recipient's response. When an acknowledgement is received, the sender sends the frame as below.
The Simplex Stop & Wait Protocol is depicted diagrammatically as follows-
3. Simplex protocol for noisy channels:
Data transfer is one-way, with a separate recipient and sender, restricted processing capacity & speed at the receiver, and errors in data frames & acknowledgement frames to be expected due to the noisy channel. Each frame has its sequence number.
The timer is initiated for a limited time after a frame is transferred. If the acknowledgement isn't received before the timer ends, the frame is retransmitted; if the acknowledgement is malformed or the transferred data frames are damaged, the sender must wait indefinitely before transmitting the next frame.
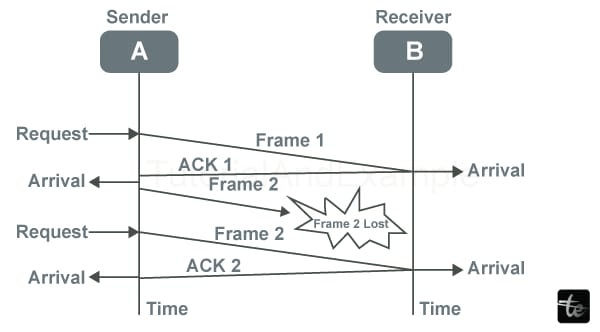
The Simplex Protocols for Noisy Channels are depicted diagrammatically as follows-
Data Link Layer Devices
The Data Link Layer employs several devices, which are described below.
Bridge: A bridge is an electrical device used in computer networking that aids in establishing connections with another bridge using a comparable protocol.
Switches: A switch is a hardware device that connects numerous devices via a network at the data link layer of the OSI model. It employs multiple packet-switching techniques to receive and send data packets across the network.
Modem: A modem is a "Modulator - De-modulator" and transfers information via telephone lines from one computer network to another.
The modulator converts all data from digital to analogue over the transmitting point and the opposite end. De-Modulators can transform analogue signals to digital signals when in reception mode.
Network Interface Card: Also referred to as a "Network Interface Controller", "Network Adapter"/"LAN Adapter". A network interface card, or a NIC, is a circuit board used in computer systems to offer a dedicated network connection.
Data Link Layer Protocol Examples:
Some Examples of Major Data Link Protocols: Wide Area Networks (WAN) and modem connections require multiple data link protocols. Logical communication Control (LLC) is a data communication protocol commonly used in LANs. Some instances of data link protocols are as follows:
List of Data Link Layer Protocols
- Synchronous Data Link Protocol (SDLC)
- High-Level Data Link Protocol (HDLC)
- Serial Line Interface Protocol (SLIP)
- Point to Point Protocol (PPP)
- Link Control Protocol (LCP)
- Link Access Procedure (LAP)
- Network Control Protocol (NCP)
- Synchronous Data Link Protocol (SDLC) is a computer communication protocol. It typically enables multipoint links as well as error recovery or repair. It is commonly used to transport SNA (Systems Network Architecture) traffic and is a forerunner to HDLC. IBM created and developed it in 1975 as well. It also connects all distant devices via point-to-point (one-to-one) Or point-to-multipoint (one-to-many) connections to centrally located mainframe computers. It also ensures that data units arrive correctly and flow from one network point to another.
- High-Level Data Link Protocol (HDLC) - HDLC is a protocol that has become a catch-all for several Wide Area protocols. It is also a component of the X.25 network. ISO conceived and developed it in 1979. In general, this protocol is built on SDLC. It also provides both unreliable best-effort service as well as accurate service. HDLC is a bit-oriented protocol that can communicate in point-to-point and multipoint modes.
- SLIP (Serial Line Interface Protocol) - SLIP is an outdated protocol that adds a framing byte to the end of an IP packet. A data link control capability is required for sending IP packets over a dial-up link between Internet Service Providers (ISPs) and residential users. It is a TCP/IP encapsulation created for communication through serial ports and multiple router connections. It has shortcomings, such as the need for error correction or detection tools.
- PPP (Point-to-Point Protocol) - PPP is a protocol that works in the same way as SLIP. It is the most resilient protocol and is utilized to transport different sorts of packets in addition to IP packets. It is also necessary for dial-up & leased router-router connections. It gives a framing mechanism for describing frames. It is a fault-detecting character-oriented protocol. It's also used to deliver two protocols: NCP and LCP. LCP is used to bring lines up, negotiate alternatives, and bring them back down, whereas NCP is used to negotiate network-layer protocols. It's needed for the same serial interfaces that HDLC.
- LCP (Link Control Protocol) - IEEE 802.2 was the first to develop and create it. It also provides HDLC-style services on local area networks (LANs). LCP is a PPP protocol for establishing, setting, testing, maintaining, and finishing/terminating links for data frame transmission.
- Link Access Protocol (LAP) - LAP protocols are data link layer protocols used for data framing and transmission over point-to-point connections. It also includes details about service dependability. LAPB (Link Access Procedure Balanced), LAPD (Link Access Procedure D-Channel), and LAPF (Link Access Procedure Frame-Mode Bearer Services) are the three versions of LAP. It is derived via IBM SDLC, which IBM has submitted to the ISP for standardization.
- Network Control Protocol (NCP) - NCP was another older protocol used by ARPANET. It allows users to use computers & various gadgets from remote locations and transmit files between two or more machines. PPP is often defined as a collection of protocols. Every higher-layer protocol supported by PPP has constant access to NCP. TCP/IP supplanted NCP in the 1980s.
Data Link Layer Functions
- Linking and Framing:
The data link layer receives each packet from the network layer, bundles it into frames, and then moves every frame bit by bit using network hardware devices. The data link layer receives every signal from hardware devices & collects them into Frame form on the receiver side.
- Addressing:
The data link layer generates the complete layer 2 addressing mechanism system, and then entire hardware addresses are identified as unique at the connection. It enables them to encode into hardware at the time of production.
- Synchronization:
After sending all frames over the link, both machines should be synchronized to communicate.
- Controlling Errors:
Some signals are having transition issues, and bits are being flipped due to a few issues. To discover those errors & precede them to recover to obtain the original data bits, it then forwards the error reporting system to the sender end.
- Flow control:
Suppose numerous stations with varying speeds or capacities are offered on the same link. With flow control, the data link layer enables both machines to interchange data at comparable speeds.
- Multi-Access:
If the host attempts to transport data over a shared link, the probability of collision increases. The data connection layer provides a CSMA/CD technique to allow various systems to access shared media.
Conclusion
We learned about the elementary data connection layer protocols, including their Types, functions, and services.