Uses Of Bridges in Computer Networks
Uses Of Bridges in Computer Networks
What are Bridges?
In computer networking, a bridge is a tool or software aspect that connects two or more local area networks (LANs) or community segments. It operates on the datalink layer of the networking protocol layer, also called Layer 2.
The primary reason to use a bridge is to ahead network site visitors between different LANs or segments while retaining them logically separate. It does this by examining the devices physical addresses, or Media Access Control (MAC) addresses, related to every LAN.
Functions of Bridges
- The basic function of bridges is to split a huge network into smaller chunks, called collision domains, to enhance network performance in general. The bridge makes it possible for devices on different segments to communicate with one another by passing network traffic between the segments.
- In addition to addressing network segmentation, extending coverage, optimising data transfer, enhancing security, providing fault tolerance, and bridging the gap between various network types, bridges also serve a variety of other functions. In the dynamic and linked digital environment of today, these functions are crucial for guaranteeing efficient and dependable network operations.
- Bridges are essential elements of computer networks that allow for efficient data transmission and seamless communication. They are essential for connecting various network segments and satisfying the rising need for interconnectivity and high-performance networks. Businesses can increase network efficiency, expand services, tighten security, and connect various network technologies by deploying bridges.
- To optimise their network architecture and fully utilise the capabilities of their computer networks, network administrators and experts must have a thorough awareness of the numerous applications of bridges.
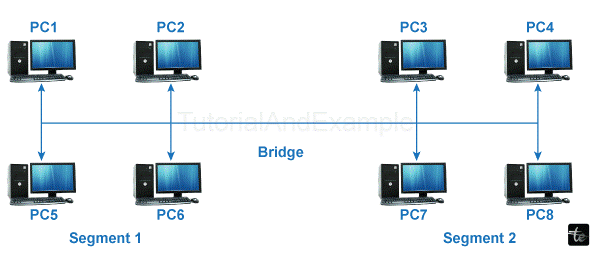
When a device wants to send information to another tool at the identical LAN, the bridge does not need to intervene. It examines the MAC addresses of the supply and destination device and decides on whether or not to go ahead with the statistics or now not.
Bridges help divide massive networks into smaller segments, improving overall performance and decreasing congestion. They additionally provide isolation and safety among LANs, as statistics mean that one LAN only wants to traverse other LANs once vital.
Knowing that "bridge" is often used interchangeably with "transfer" in present-day networking is vital. Switches are multi-port bridges capable of connecting multiple devices and LANs, providing comparable capability with additional functions and higher port densities.
Uses Of Bridges
I.Network Segmentation: Empowering Efficiency and Performance
• Explanation of the idea of network segmentation
• Decreased congestion, advanced overall performance, better security
• Role of bridges in dividing extensive networks into smaller segments
• Case research illustrating the tremendous effect of community segmentation on network performance and overall performance
II. Extending Network Coverage: Bridging the Gap
• Importance of expanding community insurance
• The function of bridges in connecting geographically remote segments
• Real-global examples showcasing using bridges to extend network attain
• Advantages of the usage of bridges for network growth rather than additional routers or switches
III. Filtering and Forwarding: Optimizing Data Transmission
• Understanding the process of filtering and forwarding data packets.
• How bridges intelligently analyze MAC addresses to determine packet destinations
• The impact of intelligent filtering on community bandwidth usage
• Real-time situations highlighting the significance of bridges in optimizing statistics transmission
IV. Interconnecting Different Network Technologies: Seamless Integration
• Importance of integrating various network technologies
• The function of bridges in facilitating communication between distinct community technology
• Benefits and challenges related to bridging distinctive community technologies
V. Enhancing Network Security:
• The vital position of bridges is in network safety
• Isolating network visitors inside character segments to defend data
• How bridges act as a security barrier in opposition to unauthorized get right to entry
• Case research demonstrating the effectiveness of bridges in enhancing network protection
VI. Fault Tolerance and Redundancy: Ensuring Reliability
• Importance of fault tolerance and redundancy in network infrastructure
• How bridges contribute to fault tolerance by way of creating redundant paths
• Real-world examples illustrating the effect of bridges on network reliability
• The function of bridges in minimizing downtime and ensuring continuous network connectivity
VII. Bridging Legacy and Modern Networks: Connecting the Past and Future -edge ones
• Understanding the challenges of integrating legacy networks
• The role of bridges in bridging the gap between legacy and current networks
• Examples of legacy community technologies that may be related to the usage of bridges
• Benefits of maintaining investments in legacy infrastructure through bridge integration
Characteristics of Network Bridges
Bridges are essential components in pc networks that possess excellent functionalities. Understanding these characteristics is essential for network administrators and professionals to make informed selections regarding community design, implementation, and optimization. In this article, we can discover the essential characteristics of bridges in computer networks, losing the light on their significance and impact on community operations.
- Compatibility: Bridges are compatible with a group of network technologies, which include Ethernet, Wi-Fi. This compatibility allows for seamless integration of network segments, irrespective of the underlying technology.
- Bridging on the Data Link Layer: Bridges perform on the OSI model's Data Link Layer (Layer 2). This layer is liable for transmitting data frames among adjacent community nodes. By functioning at this sediment, bridges can examine the MAC addresses of data packets to determine their destination and make intelligent forwarding decisions.
- MAC Address Learning: One of the vital characteristics of bridges is their capability to analyze and keep MAC addresses. When a bridge gets a data frame, it analyzes the destination MAC address and associates it with the port through which the data arrived. This method builds a MAC deal with a desk or forwarding table that's used to determine an appropriate port for forwarding future frames.
- Filtering and Forwarding: Bridges use MAC to deal with filtering to selectively ahead facts frames. If the destination deal is found at the desk, the bridge forwards the frame most effectively to the corresponding port, lowering needless network traffic.
- Spanning Tree Protocol (STP): To save you loops in community topologies, bridges hire the Spanning Tree Protocol (STP). The STP lets bridges dynamically calculate the quality direction among them, even as blocking redundant paths. By constructing a loop-loose tree structure, the STP guarantees that each bridge has the most straightforward active course to avoid broadcast storms and hold community stability.
- Segmentation and Collision Domains: Bridges allow network segmentation, which divides a huge network into smaller segments. Each section created through a bridge turns into a separate collision domain. By keeping apart collision domains, bridges specifies the community performance and reduce congestion. This segmentation also improves safety by containing ability network issues.
- Transparent Connectivity: One of the primary goals of bridges is to provide apparent connectivity to related devices. Transparent bridges function plug-and-play, requiring no configuration modifications to related gadgets. This characteristic ensures seamless integration into existing network infrastructures and simplifies community management.
- Security and Isolation: Bridges contribute to network security by keeping apart network site visitors within character segments. By preventing unauthorized get right of entry between segments, bridges act as a protective barrier, protecting touchy information and resources. They allow network directors to implement security regulations for every section, enhancing ordinary community safety.
- Redundancy and High Availability: Bridges can create redundant paths in a community, enhancing fault tolerance and community availability. Multiple bridges can make specific non-stop community connectivity, even during a bridge failure. This function enhances network reliability and minimizes downtime.
- Scalability: Bridges offer scalability in network design and enlargement. As community requirements evolve, different bridges can be delivered to deal with new segments or technology. This feature permits groups to evolve their network infrastructure to meet growing needs and emerging technology.
- Fault Isolation: Bridges contain network faults by keeping apart elaborate segments. If a fault occurs in one section, it no longer affects the operation of different segments, minimizing the impact of network disasters and facilitating easier troubleshooting.
- Broadcast Limitation: Bridges limit the propagation of broadcast visitors, preventing it from saturating the complete network. Bridges confine broadcast storms to a particular section by setting apart segments, keeping network stability.
- Collision Domain Reduction: Bridges reduce collision domain names, considering more sufficient use of network assets. By setting apart segments, bridges restrict the scope of collisions, minimizing retransmissions and enhancing essential community overall performance.