Infrared Transmission in Computer Networks
A wireless communication technology in computer networks called infrared transmission. It uses infrared light signals to transport data between units. It is appropriate for short-range communication since it enables data transmission without cables.
Infrared transmission's salient features are as follows:
- Frequency and Wavelength: Infrared waves have a frequency range of 300 GHz to 400 THz and a wavelength range of 1 mm to 770 nm. This frequency band lies within the portion of the electromagnetic spectrum that is invisible to the human eye.
- Line-of-Sight Propagation: For occurring of infrared communication, there must be a clear line of sight between the transmitting and receiving devices. This characteristic enables safe and dependable communication inside a small area.
- Data rates and bandwidth: Infrared communication provides a significant amount of usable bandwidth; however, it may have yet to be fully utilized. Up to 16 Mbp in very high data rates can be supported. Infrared transmission is appropriate for sending files and other digital data back and forth between computers.
Working of Infrared Communication in Computer Networks
Let’s see how infrared communication in computer networks operates. The infrared transmission in computer networks transmits data between devices using infrared light waves.
Here is a detailed description of how it works:
- Infrared Light: An electromagnetic radiation with a wavelength range of 1 mm to 770 nm and a frequency range of 300 GHz to 400 THz is known as infrared light. In an infrared network, data is transmitted between devices using infrared light.
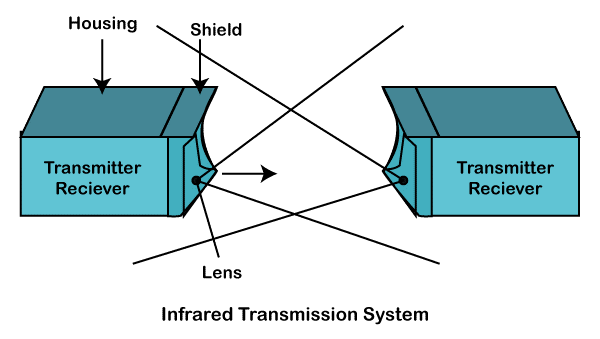
- Infrared Transmitter: A device that emits infrared light waves is known as an infrared transmitter. The transmitter in an infrared network is often found inside the sending device.
- Infrared Receiver: A device that detects infrared light waves is known as an infrared receiver. The receiver in an infrared network typically resides in the data-receiving device.
- Line-of-Sight Propagation: For infrared communication to occur there must be a clear line of sight between the transmitting and receiving devices. This characteristic enables safe and dependable communication inside a small area.
- Data Transmission: The infrared transmitter modifies the infrared light waves with the data to be conveyed to transmit data. The infrared receiver receives the modulated light waves after they have been broadcast across the air.
Some standard devices that use infrared for networking
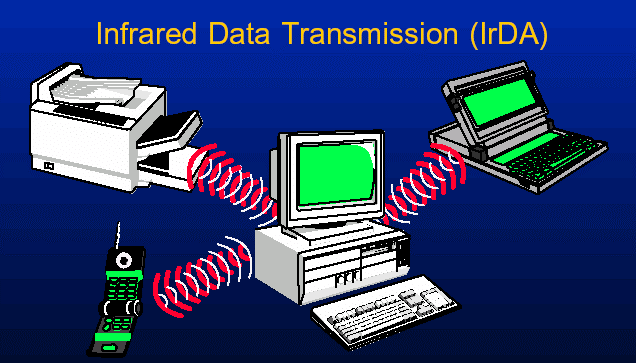
Infrared is frequently used by networking equipment like:
- Remote Control Systems: Remote control systems for televisions, VCRs, DVD players, and set-top boxes frequently employ infrared technology. Infrared light waves communicate the commands entered on the remote control to the device's receiver.
- Infrared Wireless Networking: Infrared wireless networking sends data between devices using infrared beams. Higher transmission rates are available, up to and including 10 Mbps and 16 Mbps. Instances and settings where safe and affordable cable replacement technology is required are ideal for infrared wireless networking.
- Infrared Sensors: With infrared sensors, computers can transport files and other data types using short-range wireless signals. These sensors use infrared light to communicate with other objects.
- Wireless LANs: Infrared transmission is frequently used to create fast wireless local area networks. These LANs can support very high data speeds because infrared light has a relatively large bandwidth.
Infrared technology is generally utilized in wireless LANs, infrared wireless networking, infrared sensors, and remote-control systems. These gadgets use infrared light's unique characteristics to enable wireless data transmission and communication.

Advantages of Infrared Transmission in Computer Networks
- Wireless: Without physical connections, infrared transmission enables wireless communication between devices, enhancing flexibility and mobility.
- Low cost: Compared to other wireless technologies, infrared communication components are typically less expensive, making it an economical option for some applications.
- Protection: Due to their restricted range and brutal wall penetration, infrared transmissions can offer some inherent protection by limiting the possibility of outside sources listening in.
- Reduced interference: Since infrared uses high frequencies, it is less susceptible to disruption from other wireless devices like Wi-Fi routers or Bluetooth devices.
- Low power consumption: Infrared transmission often uses less power for battery-powered devices than other wireless technologies.
Disadvantages of Infrared Transmission in Computer Networks
- Line-of-sight requirement: Direct line of sight between the sending and receiving devices is necessary for infrared transmission, which is one of the significant disadvantages. Walls or other things that impede transmission might cause signal loss and interfere with communication.
- Limited range: Compared to other wireless technologies, infrared signals have a minimal transmission range that is typically only a few meters, which can limit its suitability for use in larger network configurations.
- Susceptible to environmental conditions: Environmental influences can impact infrared signals, potentially causing interference. Examples of such influences include strong sunshine and other infrared sources.
As a result, although infrared transmission in computer networks has several significant benefits, including wireless communication, low cost, and less interference, it also has several severe drawbacks and limits, preventing its widespread implementation in contemporary networking settings. It is less useful for many applications due to its dependency on line-of-sight communication, constrained range, vulnerability to environmental factors, and lack of standardization. Compared to more established wireless technologies like Wi-Fi and Bluetooth, its usability is further constrained by the comparatively modest data transfer rates and potential security issues. Infrared transmission is rapidly being replaced by more powerful and flexible options as technology develops, making it a niche choice for particular use cases rather than a mainstream solution in modern computer networks.