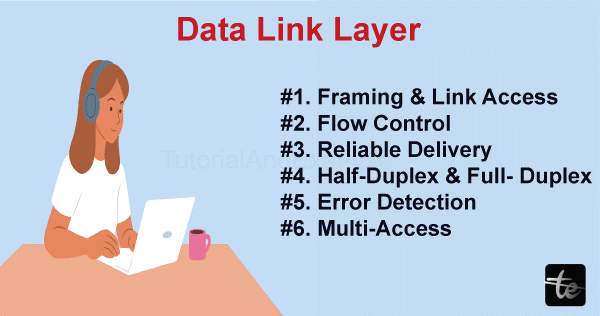
Data Link Layer services provided to the Network Layer
The data link layer provides essential services to the network layer, establishing a reliable interface between the two layers. The services offered by the data link layer are influenced by the efficiency and error rate of the underlying physical layer, ensuring effective communication between network devices.
The data link layer accomplishes those activities in the following manner :
Unacknowledged Connectionless Service: The datalink layer transmits data frames without requiring acknowledgments or establishing a connection. It suits scenarios with occasional frame loss, like broadcasting or multicast communication.
Acknowledged Connectionless Service: This service mode ensures reliable data delivery by introducing acknowledgments. The sender transmits data frames, and the receiver acknowledges their receipt. The sender retransmits the frames if no acknowledgment is received within a specified time. It provides reliability without connection overhead.
Acknowledged Connection-Oriented Service: This service mode establishes a connection between the sender and receiver before data transmission. Control messages are exchanged for error detection, flow control, and ordered delivery. It ensures reliable data transfer but includes additional overhead due to connection setup and maintenance. They are commonly used in applications requiring guaranteed delivery and sequencing, like file transfer or reliable messaging systems.
Key Elements
- Error Recovery: The data link layer consists of mechanisms to recover from errors in data transmission. If errors are detected in received frames, the data link layer can request the retransmission of damaged or lost frames from the network layer.
- Medium Access Control (MAC) Protocols: The datalink layer uses MAC protocols to control access to the shared physical medium. These protocols determine how devices contend for the medium and handle situations like collisions.
- Logical Link Control (LLC): The datalink layer provides a logical link control sublayer that interfaces with the network layer. It ensures reliable data transmission between the data link and network layers, handling tasks along with flow control, error control, and frame sequencing.
- Address Resolution: The data link layer helps translate addresses between the network and data link layers. Examples are IP addresses and MAC addresses.
- Fragmentation and Reassembly: In cases where data packets from the network layer are too large to fit in a single frame, the data link layer can break them into smaller fragments for transmission. At the receiving end, the data link layer reassembles those fragments into complete packets before delivering them to the network layer.
- Flow Control: The data link layer manages the data flow between the sender and receiver to prevent congestion and make certain data transfer. It regulates the data transmission rate to match the receiver's capacity, avoiding overwhelming the receiving device.
- Quality of Service: The data link layer prioritizes specific types of data traffic to optimize network performance for real-time applications like voice and video streaming.
- Multilink Protocols: The data link layer combines multiple physical links to increase bandwidth and enhance data transfer rates. It also enables load balancing and redundancy for more suitable network performance and reliability.
- VLAN Support: The datalink layer facilitates the creation of virtual networks within a physical network, called VLANs. VLANs provide improved network management, security, and scalability by segmenting network traffic based on logical groupings rather than physical connections.
Advantages
- Better User Experience: The services provided by the datalink layer result in an improved user experience. It is more reliable data transfers, reduced network congestion, and enhanced security for their network communications. These advantages contribute to a smoother and more efficient network experience for users.
- Enhanced Security: The data link layer enhances network security by implementing measures like MAC address filtering and VLAN segmentation. These features help control network access, prevent unauthorized data interception, and protect against various network attacks.
- Scalability and Flexibility: The ability to segment a network on the data link layer enhances scalability and flexibility. New segments can be easily added or modified as the network grows without disrupting the entire network infrastructure. This flexibility allows for future expansion and incorporation of new technologies or services without significant network-wide changes.
- Efficient Bandwidth Utilization: The data link layer efficiently utilizes network bandwidth through link management and flow control mechanisms. It ensures the most efficient transmission of data, preventing transmission and congestion. This results in advanced network performance and responsiveness.
- Support for Different Transmission Modes: The data link layer allows sending data in different ways. The data is to be sent to a specific device (unicast), to multiple devices at the same time (multicast), or to all devices on the network (broadcast). This flexibility permits efficient communication, such as video conferences, important announcements, or sharing content with multiple viewers.
- Connecting Different Network Technologies: The data link layer bridges various network technologies, ensuring smooth integration. It enables data transmission between different types of networks, like Ethernet and Wi-Fi, facilitating communication across environments. This allows devices with different technologies to communicate efficiently.