Functions of the Transport Layer
The Transport Layer is in charge of facilitating dependable and effective communication between network end systems (computers). In addition to providing capabilities like flow management, congestion control, and multiplexing, its main purpose is to assure the dependable transportation of data throughout a network.
The Transport Layer's primary responsibilities are as follows:
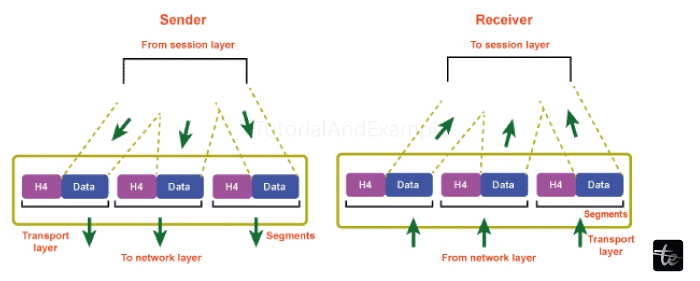
Segmentation and Reassembly
Segments or datagrams are used by the transport layer to divide the data received from protocols at the top layers (such as the application layer) into smaller chunks. Due to the network layer's (IP) maximum payload size and the transport layer's adaptation of the data to fit within these restrictions, segmentation is required. In order to ensure that the data is delivered to the right application in the right order, the transport layer reassembles the segments into the original data stream at the receiving end.
Connection Control
Connections between source and destination hosts are established, maintained, and terminated via the Transport Layer. It controls the creation and dissolution of logical connections, ensuring the efficient and reliable interchange of data.
Flow Control
The transport layer uses flow control to regulate the rate of data transmission between the sender and recipient. It guards against a quick sender or a busy network overwhelming the recipient. The sliding window method used by TCP allows the receiver to inform the sender of its buffer capacity. The sender then modifies the transmission rate in accordance with the amount of buffer space that is accessible, guaranteeing effective data flow without taxing the receiver. In order to prevent the receiving host from becoming overloaded, the transport layer controls the data flow between the sender and receiver. In order to control the rate of data transmission and avoid congestion, it employs a variety of strategies, including sliding window protocols.
Error Control
Errors that could happen while transmitting data must be found and fixed by the transport layer. Checksums, where a checksum value is computed at the sender and supplied in the segment header, are often used to detect errors. The receiver runs the identical calculation and contrasts the computed and received checksums. If a mismatch is found, it means that a transmission error took place. In these circumstances, the receiver may ask the sender to send the corrupted section again. The transport layer uses mechanisms for error detection and repair to guarantee the data is delivered reliably. To accomplish error-free data transfer, it makes use of techniques like checksums to identify problems in the data that has been received and retransmission of lost or corrupted segments.
Congestion Control
By controlling the flow of data when the network is overcrowded, congestion management prevents network congestion. In order to alleviate congestion and maintain optimal performance, it uses a variety of algorithms to monitor network conditions, detect congestion, and change the transmission rate.
Multiplexing and De-multiplexing
Multiple apps or services can use the network at once thanks to the Transport Layer. Each application or service is given a specific identification (port number), which enables the Transport Layer to multiplex many data streams into a single network connection. These identifiers are used to de-multiplex incoming data and send it to the correct application at the receiving end.
Quality of Service (QoS)
The Transport Layer can offer Quality of performance (QoS) methods to priorities particular traffic types or ensure a given level of performance for particular applications. Bandwidth distribution, latency management, and the prioritization of urgent or important data are examples of QoS features.
Connection Establishment and Termination
Mechanisms for establishing and severing connections between hosts are provided by the transport layer. A three-way handshake is needed to create a trustworthy connection in the case of connection-oriented protocols like TCP (transfer Control Protocol) before data transfer can start. To synchronize sequence numbers and set connection parameters, this method entails the transmission of control messages between the source and destination hosts. A connection termination phase is started once the communication is finished in order to kindly terminate the connection and release the resources.
Reliable Data Transfer
An essential feature of the transport layer, especially in TCP, is reliable data transfer. It guarantees that information sent over the network is received precisely and in the proper order. TCP makes use of timers, sequence numbers, and acknowledgment methods to accomplish this. Segments are sent, and the sender waits for messages from the recipient confirming receipt. The sender resends the segment if an acknowledgment is not received within a predetermined amount of time. Up till all segments have been successfully transmitted and recognized, this process is repeated.
Conclusion
In conclusion, the transport layer is crucial to network communication because it offers services for multiplexing and de-multiplexing, segments and reassembles data, establishes and terminates connections, ensures dependable data transfer, implements flow control, manages error detection and correction, and manages network congestion. Together, these features allow apps on various networks to communicate effectively and robustly.