Types of Ethernet in Computer Networks
Introduction
Ethernet is a networking technology that consists of the computer chip, port, protocol, and connection required to connect a desktop or laptop to a local area network (LAN) for fast data transfer using fiber optic or coaxial cables.
Xerox created Ethernet, a wired connection-based communication technology, in the 1970s to connect computers in a network. It links systems on the wide area network (WAN) and local area network (LAN) (WAN). Many equipment, including laptops and printers, can be connected across homes, businesses, and even small communities via LAN and WAN.
History of Ethernet
Early in the 1970s, a team led by David Boggs and Robert Metcalfe at the Xerox Palo Alto Research Centre (PARC) invented Ethernet. In 1983, the Institute of Electrical and Electronics Engineers (IEEE) adopted it as a standard. Metcalfe developed the idea for Ethernet in a 1973 document he wrote for Xerox PARC, which formed the foundation for the network's first development. The Aloha system, an earlier networking effort started in 1968 at the University of Hawaii, served as the foundation for Metcalfe's development of Ethernet. After determining that the system had outlived its original designation, Alto Aloha Network, Metcalfe renamed it Ethernet in 1973.
After four years, Metcalfe and Boggs, along with Charles Thacker, Butler Lampson, and their associates at Xerox, were able to successfully trademark Ethernet technology. In 1980, Intel, Xerox, and Digital Equipment Corporation collaborated to create the first 10 Mbps Ethernet standards. An analogous open standard was being developed in the interim by the IEEE Local and Metropolitan Area Networks (LAN/MAN) Standards Committee. An Ethernet subcommittee was established by the LAN/MAN committee and assigned the number 802.3. The IEEE accepted the original 802.3 thick Ethernet specifications in 1983, and they were formally published in 1985.
Working of Ethernet
The Ethernet protocol's star topology, also known as the linear bus, serves as the foundation for the IEEE 802.3 standard. The physical layer and data link layer, the first two tiers of the OSI network hierarchy, are where this protocol functions. The two distinct levels that comprise the data connection layer in Ethernet are the logical link control tier and the medium access control (MAC) tier.
The primary job of the data connection layer in a network system is sending data packets between nodes. Ethernet has an access method called CSMA/CD (Carrier Sense Multiple Access/Collision Detection) that enables each computer to listen to the connection before transferring data over the network. Ethernet also transports data using packets and frames.
In addition to the provided data payload, the frame contains the following data:
- The physical addresses and MAC of the sender and receiver Error-corrected data to identify gearbox defects.
- Information about virtual LAN (VLAN) tagging and quality of service (QoS) Several bytes of data are sent in each packet to establish the connection and identify the start point of the frame
Features of Ethernet
- Speed: Current Ethernet standards offer up to 100 Gbps of data transmission, demonstrating Ethernet's high-speed data transmission capabilities.
- Flexibility: Ethernet may be utilized with a wide array of devices and operating systems, making it a flexible technology. Additionally, it is easily scalable to support an increasing number of devices and users.
- Reliability: Ethernet is a dependable technology that makes use of error-correction methods to guarantee precise and effective data transmission.
- Cost-effectiveness: Ethernet is a widely available, inexpensive technology that is simple to use.
- Security: Ethernet has built-in security mechanisms, including authentication and encryption, to prevent unwanted access to data.
- Manageability: Network managers may monitor and regulate network traffic with ease using a variety of tools available for Ethernet networks.
- Compatibility: Ethernet is easily integrated with other systems and devices due to its broad compatibility with a variety of other networking technologies.
- Availability: Ethernet is a widely accessible technology that can be utilized in a wide range of environments, including big data centres, small and home offices, and enterprise-level networks.
- Simplicity: Ethernet is a straightforward technology that is simple to use and comprehend. A broad spectrum of users can set it up and configure it without the need for specific knowledge or experience.
- Standardisation: Since Ethernet is a standard technology, all Ethernet systems and devices function as a whole. This facilitates network administrators' management and troubleshooting of Ethernet networks.
- Scalability: Ethernet's great scalability allows it to readily handle the addition of more users, devices, and applications without compromising on reliability or speed.
- Broad compatibility: TCP/IP, HTTP, FTP, and other protocols and technologies are only a few of the many that Ethernet is compatible with. Because of this, it is a flexible technology that may be applied in a range of contexts.
- Ease of Integration: Ethernet is easily combined with other networking technologies, like Bluetooth and Wi-Fi, to form a seamless network environment.
- Ease of troubleshooting: A variety of integrated diagnostic and monitoring tools make troubleshooting and diagnosing Ethernet networks simple. This facilitates the rapid and effective identification and resolution of problems by network managers.
- Multimedia support: Ethernet is perfect for environments where multimedia content plays a significant role in the user experience since it can handle multimedia applications like streaming music and video. Ethernet is a popular, dependable, and reasonably priced local area network (LAN) technology that provides fast connectivity and simple management for local networks.
Components of an Ethernet Connection
What is included in an Ethernet connection is as follows:
- Xerox created the Ethernet protocol in the 1970s. As previously explained, it is a set of standards that regulates the data flow between Ethernet components.
- Ethernet ports: Also called jacks or sockets, Ethernet ports are openings in computer network hardware that accept the plugging of Ethernet cables. Supported cables have RJ-45 connectors. The Ethernet connector on the majority of computers is used to connect the device to a wired connection. An Ethernet network adapter, often known as an Ethernet card, is installed on the motherboard and linked to the Ethernet port of a computer. A router may have several Ethernet ports to support various wired network devices.
- Ethernet network adapter: An Ethernet adapter is a chip or card that slides into a motherboard slot to connect a computer to a local area network (LAN). Previously, these were only used with desktop computers. These days, motherboard chipsets for laptops and desktop computers have Ethernet.
An Ethernet cable, also called a network cable, is used to link your computer to a router, modem, or network switch. The Ethernet cable is composed of the RJ45 connector, plastic jacket, and internal wiring.
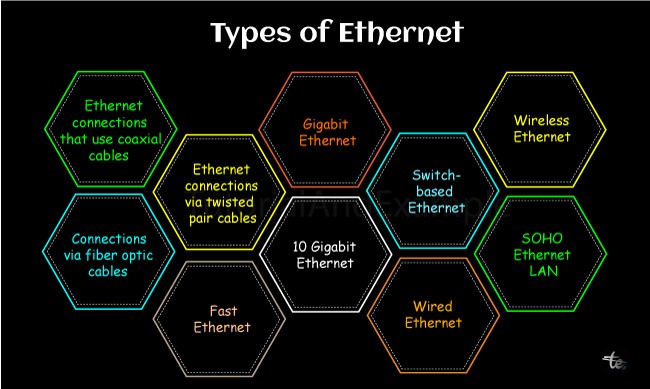
Types of Ethernets
The following are the main categories of Ethernet connectivity:
Ethernet connections that use coaxial cables
Electrical signals can be transmitted at high frequencies with little loss using coaxial wire. Ethernet types 10Base2 and 10Base5 are currently in use. A dielectric insulator, generally made of Teflon or PVC, encloses a copper conductor. A conductive metallic shield that is braided around the dielectric insulator reduces both external and metal electromagnetic interference. The metallic shield is then wrapped in a sheath made of PVC or another type of fire-resistant plastic. Its maximum transmission speed is 10 Mbps.
Additional classifications for this Ethernet type include networks that employ one of the following cable types:
- Tri-axial: This Ethernet variation provides more bandwidth and resilience to interference by using an additional copper braid shield. It is commonly used to link cameras and cable televisions.
- RG-6: This type of coaxial cable can improve signal quality in cable television, wireless broadband, and other applications. It has a thicker dielectric insulator.
- Hardline: This type of cable is used in Ethernet networks that require a strong signal. It's also used in internet and phone connections.
Connections via Fiber Optic Cables
These connections use optical fibers with glass cores that are covered in several Teflon or PVC cladding sheets. Fiber optics has no interference issues because it transmits data as light signals.
Compared to twist pairs and coaxial cables, fiber optics can transmit signals over much longer distances. It uses Ethernet versions 10BaseF, 100BaseFX, 100BaseBX, 100BaseSX, 1000BaseFx, 1000BaseSX, and 1000BaseBx. As a result, it can send data quickly.
The following methods can also be used to partition this type of Ethernet into networks:
- Single-mode fiber (SMF): This type of fiber is used for long-distance communication and transmits data via a single light beam.
- Multi-mode fiber (MMF): This option is less expensive than others and transmits data using multiple light beams.
Ethernet Connections via Twisted Pair Cables
In order to minimize crosstalk and interference, twisted pairs of copper wires are made up of two insulated copper wires wrapped around one another. It makes use of 10BASE-T, 100BASE-T, and a few other more modern Ethernet variations.
Use of RJ-45 plugs is made. There are a few possible versions for this Ethernet type:
- Shielded twisted pair (STP) cables are used in Ethernets; these cables protect against interference from entering or leaving the cable. As a result, they are utilized at faster transmission rates and over longer distances.
- Networks that employ unshielded twisted pair (UTP) cables: UTP cables are currently among the most widely used cables in computer networks. Two insulated, twisted copper wires make up a UTP; twisting cables reduce interference.
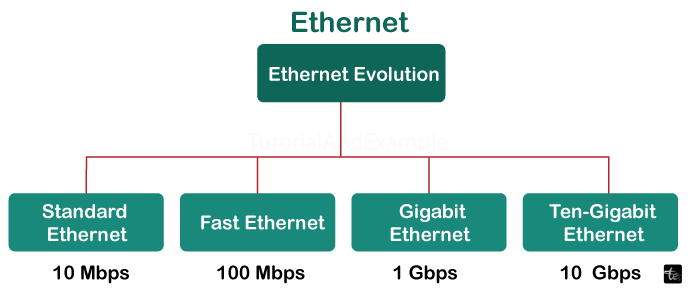
Fast Ethernet
It is an Ethernet network with a data transmission speed of 100 Mbit/s. Fibre optic cables or twisted pairs may be used. (While still in use, the older 10 Mbit/s Ethernet does not provide the bandwidth needed for some network video scenarios.)
A 100BASE-TX/10BASE-T Ethernet interface, also called a 10/100 interface, is found on most network-connected devices, such as laptops and network cameras. This interface supports Fast Ethernet and 10 Mbit/s. Fast Ethernet is made possible via Cat-5 twisted pair cables.
Gigabit Ethernet
Gigabit Ethernet has a data transfer rate of one gigabit per second (1 Gbit/s) and is becoming more and more common. It may also be based on a twisted pair or fiber optic connection. In the near future, it is expected to become the de facto standard, surpassing Fast Ethernet.
Gigabit Ethernet uses all four types of twisted wires to achieve high data speeds. It is made possible by Cat-5e twisted pair cables. Networked video systems are recommended to use Cat-5e cables or higher. The majority of interfaces are commonly referred to as 10/100/1000 interfaces since they are compatible with both 10 and 100 Mbit/s Ethernet.
10 Gigabit Ethernet
With an optical fiber or twisted pair connection, 10 Gigabit Ethernet, the most recent version of the Ethernet protocol, can achieve 10 Gbit/s (10,000 Mbit/s) of data throughput. When constructed on an optical fiber link, 10GBASE-LX4, 10GBASE-ER, or 10GBASE-SR might span up to 10,000 meters (6.2 miles). For the twisted pair option, excellent-quality cable (Cat-6a or Cat-7) is needed. Ethernet 10 Gbit/s is mostly used for backbone networks in high-end businesses where large data speeds are required.
Switch-based Ethernet
This network setup includes a switch or hub and a regular network cable instead of a twisted pair cable. A network switch's main function is data transfer between devices on the same network. Since data is moved from one system to another without endangering other networking hardware in the same environment, a network switch effectively completes this task.
This type of Ethernet network is switch-centered and features a star topology. Unlike gateways, which have long used similar filtering and switching processes, network switches use these techniques.
Wired Ethernet, which uses cables
The most common kind of wired LAN or WAN connectivity is this one. For solo users, this is actually a great option for an Internet connection.
In a small business network, for example, this is also possible for multiple users. A network of this kind can connect one to fifteen devices over a distance of up to ten kilometers. Even if wired Ethernet is all but obsolete, smaller groups can still benefit from it since it is quicker and more secure than wireless networks. It can load and transfer massive amounts of data including audio and video and stream them live without any interruptions.
Wireless Ethernet
A wireless network connects a receiving device, such as a laptop, to the network wirelessly using high-frequency radio signals rather than cables. This technique, which is sometimes referred to as Wi-Fi, transfers data wirelessly rather than through a cable. As a result, it may be adjusted more easily than wired networks and a device will connect if it is nearby or within the router's and modem's perimeter.
If a modem and router are present, an Ethernet category 5 (Cat5) or category 6 (Cat6) connection is required to link them. The routers send a signal to the virtually linked item. Setting up this network is easy, although the wireless signal can be problematic.
SOHO Ethernet LAN
A small office or home office is referred to as a SOHO. This is the most basic Ethernet LAN configuration.
To capitalize on this necessity, vendors provide integrated networking connections that serve as Ethernet switches and routers. These devices usually have four to eight LAN access points. Certain variations also feature wireless LAN entry points, also known as access points.
Advantages of Ethernet
- Enhances user experience with the Internet: Many of them install Ethernet connections in their houses when the speed of their Wi-Fi data connection is too low. When connecting many devices in a wide area network (WAN) or local area network (LAN), Ethernet is usually utilized.
- Offers many speed options according to needs, price, and location: Fast Ethernet has a top speed of 100Mbps, Gigabit Ethernet has a top speed of 1Gbps, and 10 Gigabit Ethernet has a peak speed of 10Gbps.
- Achieves a balance between performance and cost: Ethernet is extensively utilized since it is inexpensive and works with all future network devices. In 1983, the speed of Ethernet was about 10Mbps; today, it is more than 400Gbps. Because of its quick speed, reliable network security, and affordability, Ethernet is widely utilized by businesses, healthcare facilities, educational institutions, and online gamers.
- Expands the capabilities of your Wi-Fi network: Wi-Fi has grown in popularity over the past few years. Technology advancements have led to increased Wi-Fi coverage and faster speeds. A finite number of devices can only be supported concurrently by Wi-Fi transmissions. Ethernet connections are crucial in older buildings that may have Wi-Fi dead zones.
- Ensures higher security: Ethernet is more secure than Wi-Fi.
- Facilitates direct current (DC) power transmission: As the name suggests, power over Ethernet (POE) refers to the delivery of energy supply via Ethernet connections. Numerous gadgets, such as wireless access points and CCTV cameras, are powered by it. One of its main benefits is that it eliminates the need for a separate power supply. This is especially helpful for putting electronics in distant places with limited access to power.
Disadvantages of Ethernet
- Distance restrictions: A conventional Ethernet network's maximum cable length is 100 meters. Ethernet has certain restrictions. This implies that larger networks requiring longer lengths would find it unsuitable.
- Bandwidth sharing: When more devices are joined to an Ethernet network, the bandwidth available to each device is shared, thus lowering network speeds.
- Security flaws: Ethernet is susceptible to security lapses, such as illegal access and data interception, despite having built-in security measures.
- Compatibility problems: Although Ethernet is generally compatible with other networking technologies, there may be problems when integrating it with legacy or older systems.
- Physical constraints: Since Ethernet networks need physical connections between devices, network design flexibility and mobility may be restricted.
Conclusion
Ethernet is still useful even in the age of fast wireless connectivity, especially with the introduction of Wi-Fi 6. The majority of homes have an Ethernet connection connected to their hub or router since it is still the most effective way to access the Internet in many areas. Even though Ethernet switches have been available for a while, the market is still expanding. Ethernet is an essential component of businesses' networking infrastructure. You can maximize the performance of wired internet connections by being aware of how Ethernet operates.