FDDI in Computer Network
In the dynamic realm of computer networking, FDDI is an acronym that stands for “Fiber Distributed Data Interface”. While it may not be as widely recognized as some of its counterparts, the significance of FDDI in the context of computer networks cannot be overlooked.
FDDI, an acronym for Fiber Distributed Data Interface, represents a pivotal chapter in high-speed data transmission. This article delves into the intricacies of FDDI, examining its core principles, architecture, and relevance in today's rapidly evolving digital landscape. By the end of this exploration, you'll gain a deeper understanding of FDDI's role in ensuring robust and reliable data connectivity.
What is FDDI?
FDDI, or Fiber Distributed Data Interface, represents an advanced networking technology significantly influencing high-speed data transmission. Its inception can be attributed to the demand for dependable and swift data communication, with its origins dating back to the 1980s when organizations recognized the increasing need for resilient networking solutions.
FDDI is characterized by its utilization of a unique dual-ring topology at its core, setting it apart from conventional networking technologies. This architecture consists of two interwoven rings, the primary and secondary rings, operating in opposite directions.
A defining characteristic of FDDI is its reliance on fiber optic cables for data transmission. Fiber optics enable FDDI to achieve remarkable speeds, surpassing traditional copper-based cabling systems. This reliance on fiber optics facilitates high-speed data transfer and makes FDDI less susceptible to electromagnetic interference, further bolstering its reliability.
FDDI's history and architecture make it a robust and dependable choice for organizations seeking top-tier network performance and fault tolerance. Its use of fiber optics and dual-ring topology has made it a formidable contender in computer networking.
FDDI Features and Benefits
FDDI boasts an array of advantages that make it a compelling choice in computer networks. Its unique features and benefits address the core needs of organizations seeking robust and dependable networking solutions.
FDDI excels in high-speed data transmission, thanks to its utilization of fiber optic cables, which enable it to achieve impressive data transfer rates that outpace the capabilities of conventional copper-based networks. This exceptional speed ensures the seamless operation of data-intensive applications like video streaming and large file transfers, eliminating performance bottlenecks.
Moreover, FDDI is celebrated for its fault tolerance. Its dual-ring topology allows for network redundancy, ensuring uninterrupted data flow even in the face of cable damage or node failures. In the event of a fault, the network swiftly reroutes data through the secondary ring, minimizing downtime and data loss. This resilience is especially critical for organizations where network reliability is paramount.
Scalability is another notable feature of FDDI. It accommodates the growth and evolving needs of organizations by allowing the addition of more nodes and devices to the network. This scalability is essential in dynamic environments where expanding the network infrastructure is a recurring necessity.
Comparing FDDI to other network technologies, such as Ethernet, reveals distinct differences. While Ethernet is prevalent and cost-effective for local area networks (LANs), FDDI's strength lies in its suitability for wide area networks (WANs) and mission-critical applications. FDDI's high-speed capabilities and fault tolerance make it an excellent choice for organizations without network downtime and requiring exceptional data integrity.
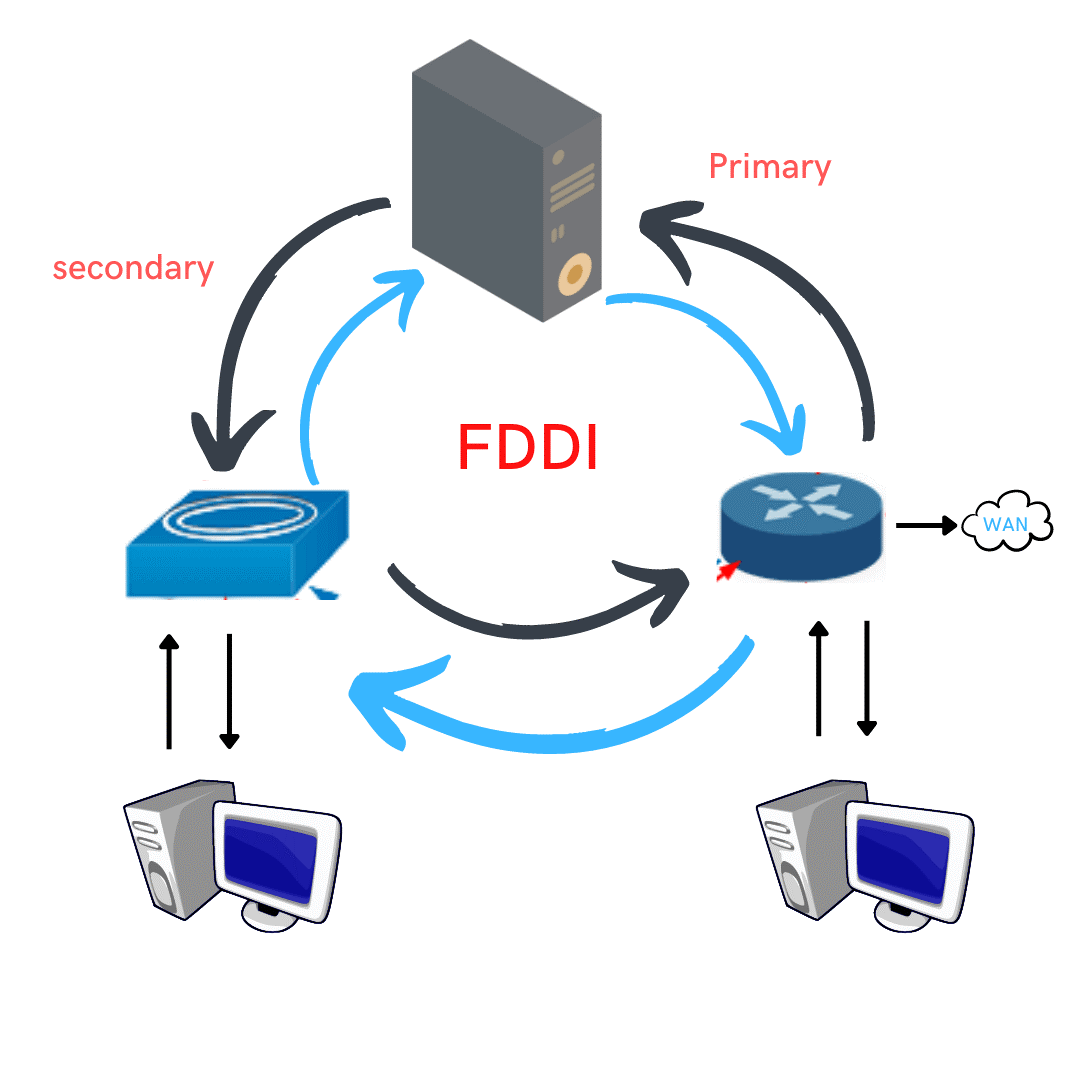
Fig: Fiber Distributed Data Interface
FDDI Architecture
At its core, an FDDI network is characterized by its dual counter-rotating rings. This architecture consists of two interconnected rings: the primary ring and the secondary ring. Data packets traverse these rings in opposite directions, enhancing network reliability and providing fault tolerance. If a cable break or node failure occurs in the primary ring, the network quickly switches to the secondary ring, ensuring uninterrupted data transmission. This dual-ring design is a pivotal feature of FDDI, safeguarding against downtime.
Concentrators and stations are integral components within an FDDI network. Concentrators, also known as dual-attached concentrators (DACs), serve as central hubs that manage the connections between stations. Stations are the endpoints within the network, such as computers or network devices, that communicate with each other through the concentrators. Concentrators streamline network management, making adding or removing stations easier without disrupting the entire network.
Data flows through the network in a token-passing manner. A token, a special packet, circulates through the network, permitting stations to transmit data. This orderly process prevents data collisions, ensuring efficient data transmission. When errors are detected in data packets, FDDI employs error-handling mechanisms to rectify the issues. These mechanisms include retransmitting corrupted packets, ensuring data integrity, and minimizing data loss.
In essence, FDDI's architecture provides:
- A resilient and reliable foundation for data transmission with its dual counter-rotating rings.
- The role of concentrators and stations.
- Its token-passing data flow mechanism.
This architecture's fault tolerance and error-handling capabilities make FDDI a formidable choice for mission-critical networking environments.
FDDI Standards and Variations
Within the realm of Fiber Distributed Data Interface (FDDI), we encounter distinct standards and variations, each crafted to address specific networking requirements.
FDDI-1, the original FDDI standard, has remained the bedrock of this technology from its very beginning. With a data rate of 100 Mbps (megabits per second), FDDI-1 fulfils the demand for swift data transmission in typical network settings. It is a trusted choice for organizations seeking fast and dependable connectivity within their local area networks (LANs).
In contrast, FDDI-2 offers a variation that steps up the game, providing data rates of up to 200 Mbps. This standard finds its niche in scenarios demanding exceptionally swift data transfer. It shines in applications like multimedia or video conferencing, where the transmission of substantial data volumes must occur promptly and without hiccups.
The differentiating factor between these standards primarily lies in their data rates and designated use cases. FDDI-1, with its 100 Mbps speed, suits general-purpose LANs and standard network applications. In contrast, FDDI-2, with its 200 Mbps capacity, excels in specialized environments requiring higher bandwidth, making it an excellent fit for multimedia and data-intensive applications. This flexibility empowers organizations to select the standard that aligns perfectly with their unique networking needs, ensuring optimal performance and efficiency.
Applications of FDDI
FDDI (Fiber Distributed Data Interface) finds its application in a diverse array of real-world scenarios, showcasing its versatility and reliability across various industries.
- Telecommunications: In the telecommunications sector, where uninterrupted data transmission is paramount, FDDI plays a critical role. It ensures high-speed and fault-tolerant data transfer, making it ideal for handling the vast volumes of data in telephone and internet networks. FDDI's resilience guarantees minimal downtime, which is crucial for maintaining constant communication services.
- Finance: The finance industry heavily relies on secure and swift data exchanges for activities such as online trading, banking transactions, and financial data analysis. FDDI's high-speed data transmission and redundancy features ensure that critical financial data is transmitted quickly and reliably, even during peak trading hours or in the event of network disruptions.
- Healthcare: In healthcare, where patient records, medical imaging, and real-time monitoring demand immediate access to data, FDDI's capabilities shine. It supports the rapid transfer of large medical files and images, enabling healthcare professionals to make informed decisions promptly. Moreover, FDDI's fault tolerance ensures that crucial patient data remains accessible without interruption.
- Education and Research: Educational institutions and research facilities benefit from FDDI's robustness. It allows for seamless collaboration and sharing of research data, facilitating innovative breakthroughs. Its scalability accommodates the growth of research networks, ensuring that data-intensive projects run smoothly.
- Government and Defence: Government agencies and defence organizations rely on secure and dependable networks for critical communications and data sharing. FDDI's fault tolerance and high-speed capabilities make it a preferred choice for safeguarding sensitive information and maintaining constant connectivity, even in challenging conditions.
- Manufacturing and Industrial Control: FDDI is instrumental in industrial automation and control systems, where real-time data transfer is essential for monitoring and managing complex manufacturing processes. Its ability to withstand electromagnetic interference ensures the reliability of data communication in industrial settings.
Challenges and Limitations
While FDDI (Fiber Distributed Data Interface) boasts impressive capabilities, it has its set of challenges and limitations that warrant consideration.
- Cost: One of the primary challenges associated with FDDI is its cost. The installation of fiber optic cabling and the requisite hardware can be expensive. This cost factor can deter smaller organizations with budget constraints from adopting FDDI, opting for more affordable alternatives like Ethernet.
- Compatibility: FDDI's unique architecture and reliance on fiber optics can pose compatibility issues with existing network infrastructures. Integrating FDDI into an older network may require significant investments and modifications, adding complexity to the migration process.
- Complexity: The dual-ring topology, while providing redundancy, can introduce complexity in network management. Configuration, maintenance, and troubleshooting may require specialized expertise, increasing operational costs.
- Limited Market Availability: As newer networking technologies continue to emerge, FDDI's market availability has diminished. Finding FDDI-compatible equipment and skilled professionals to support it can become increasingly challenging.
- Bandwidth Limitations: Despite its high-speed capabilities, FDDI's bandwidth may need to be improved for modern data-intensive applications and high-traffic networks. In comparison to newer technologies like gigabit Ethernet and beyond, FDDI may still need to meet the bandwidth demands of certain applications.
- Migration Challenges: Organizations using legacy FDDI networks face migration challenges when transitioning to newer technologies. This transition often requires careful planning, substantial investment, and minimal disruption to ongoing operations.
Conclusion
In conclusion, this article has explored the intricate world of FDDI (Fiber Distributed Data Interface), highlighting its significance and diverse applications in computer networking. FDDI's unique attributes, including high-speed data transmission, fault tolerance, and scalability, make it a resilient choice for critical network environments.
As the digital landscape continues to evolve, FDDI remains a testament to the enduring importance of reliable data connectivity. Its dual-ring architecture and reliance on fiber optics set it apart, ensuring uninterrupted data flow.