Multicast Routing Protocols in Computer Networks
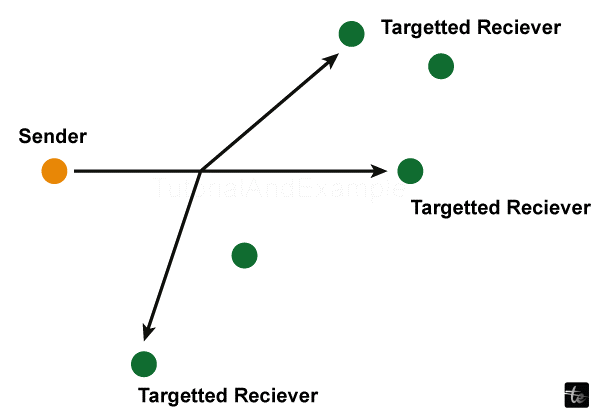
Multicast is a group communication mechanism in which the sender distributes data to several network nodes or recipients at the same time. Multicasting is a sort of one-to-many and communication between many people in which the sender or senders deliver data packets to several recipients simultaneously over LANs or WANs. This approach helps to reduce the network's data frame by allowing numerous nodes to receive data at the same time.
Multicasting is regarded as a specific instance of broadcasting. It functions similarly to Broadcasting, however with multicasting, information is delivered to individual people in the network. This operation can be completed by delivering separate copies to every user or node in the network; but, doing so is wasteful and may increase network latency. To address these drawbacks, multicasting enables for a single broadcast to be shared among numerous users, reducing the signal's capacity.
What is the purpose of multicasting?
The major purpose Multicasting transmits just one copy of a packet of data to specific destinations, ensuring that only machines that request the data receive it. Before arriving, routing tables check endpoints to make sure they're at the right address.
In contrast, unicasting transmits one packet to a single source, and broadcasting sends single packet to all sources at the same time.
This selective delivery serves several purposes. First, it optimizes the loop-free topology, enabling the protocol to find the shortest path for data receipt. Second, it only sends data packets once, hitting node again if they make requests.
Multicast has reduced bandwidth needs since it just delivers one information stream. This makes it excellent for handling massive amounts of data across multiple software and technologies, such as media.
There is the possibility of increasing or decreasing bandwidth use because not all recipients will make persistent queries if they missed the multicast. However, persistent efforts by a few individuals may boost traffic.
Finally, multicasting is particularly scalable since it makes data available to a huge number of individuals without the complexities of a broadcast. It should spread traffic such that it is easy to monitor, reducing congestion and providing space for support interference as necessary.
Working of Multicast Routing
Multicast networking begins by transmitting data to a select set of receivers, who then filter it to additional necessary receivers, such as tree branches. This is why these configurations are sometimes referred to as multicast trees.
Another method multicasting minimizes latency and bandwidth is by not attempting to send more messages than it is capable of handling. Diversifying the nodes in charge of disseminating information allows receivers to obtain data quickly.
Multicasting necessitates servers capable of supporting many protocols. Otherwise, it will not work properly over LANs or WANs. Routers use protocol independent multicast (PIM) and internet group management protocol (IGMP) to create tree branches and access data. IGMP notifies multicast rendezvous points about the number of receivers and their location.
Multicast Routing Protocols
Several routing methods improve multicasting performance, but the most common are dense mode, sparse mode, and reverse path forwarding.
Dense Mode
The dense mode distributes data to all subnets of the multicast network. This is also known as flooding since it transmits packets using fewer discretion compared to other protocol variations.
However, not all routers are required to accept this package. Prune messages can warn the transmitting nodes and prevent them when receiving information, reducing needless data emissions.
The PIM protocol can function in dense style multicast routing because it generates as many short paths to receivers as feasible.
Sparse Mode
In contrast to dense mode, which delivers data in bulk to linked networks, sparse mode takes just the time to If a request is made, carry it out.
Protocols like this one decrease bandwidth utilization while also allowing nodes in the multicast network to get information over time if they make a specific request.
A PIM sparse model, similar to dense mode, exists.
Reverse Path Forwarding
Reverse route forwarding uses a self-check to ensure that nodes do not get the same data they gave, as the sender will not look at the interface in question.
Although multicast routing improves for short pathways, it can occasionally cause loops when packets repeatedly reach other linked nodes. In some circumstances, it may mistakenly squander resources by returning data to the initial sender. Reverse route forwarding enables more purposeful data transmission and reception.
Multicast Tree Classification
Two multicast routing classes highlight the protocol's flexibility: source-based tree (SBT) and group shared tree (GST). They also emphasize the need of multicast routing in conjunction with other protocols for goal optimization.
Source-Based Tree (SBT)
- In an SBT technique, the starting point of the multicast routing generates a tree, with each group traceable back to the originating source. At identical time, because each node is still communicating the source, it might continue to produce new branches.
- SBTs are marked as source and group (S, G). They try to find the shortest path to as many recipients as possible, reducing the distance that data goes each time it is sent. Thus, it is often referred to in the shortest-path tree (SPT).
Group Shared Tree (GST)
- GSTs route packets from numerous sources to a rendezvous point (RP). The RP then passes the packets up the shared tree.
- GSTs are marked as (, G), with an asterisk () replacing the source, as the source might be a variety of other origins outside the RP.
- This configuration allows for bidirectional transmission. As a result, not every member is required to be connected to the initial router or core.
Multicast Routing Supported
Multicast networking is not enabled by default and might not be supported on all networks. Where backed, users can turn it on and off via network settings. You may set up your router to handle any multiplex routing protocol. The host is subsequently given an Internet Protocol (IP) address that users downstream may easily recognize.
It employs a multicast forwarding information base (MFIB) to deliver data to the routing information base (MRIB). These maintain open contacts with other protocols while tracking data transfer speed and bytes.
Examples of Multicasting
- Multicast routing is used in a variety of applications, including IPTV media streaming, video conferencing, file shipping, and Internet of Things (IoT) sensors.
- Contextualizing multicasting using these examples may help you grasp its most relevant usage and what distinguishes it from other routing methods. Even if unicasting or broadcasting is sufficient to convey media or large volumes of data, it might not always be the best option.
- Streaming: One of the most popular multicasting applications, it allows video or other media to be broadcast to users throughout a corporate campus as well, school, or hotel complex. Multicasting may also be used to live broadcast events like concerts.
- Videoconferencing: Using Zoom calls Multicasting, similar to mass training videos sessions, allows a large number of participants to engage in the same activity without overloading the server.
- File Distribution: Over-the-air patch management, OS system images, and even financial market tickers can all be broadcast via corporate networks.
- When IoT devices collect data, the sensors included in them translate and send it to databases, artificial intelligence, and a variety of other sources. Such systems can depend on broadcasting to monitor cybersecurity and verify proper receivers.
- Multicasting might be used for large-scale educational experiences and gaming events in virtual reality. The possibilities are growing as new technologies enter the picture, pushing the boundaries of what and the way multicasts may transmit experience across networks.
- It is worth noting that content delivery networks (CDNs) such as Netflix have many properties with multicasting, they are often implemented using unicast. Although this may raise latency on the organization's home network, it allows for greater flexibility in distributing material on demand via the internet.
Conclusion
In conclusion, Multicast routing is a technology that distributes a single copy of data to several users on a closed network. Multicasting is most commonly used for videoconferencing and media streaming on corporate networks like hotels or universities.The multicast routing protocolis required for handling current technology purposes such as videoconferencing and meeting demand for data as it grows from workers who work remotely to a more tech-savvy younger population. Routers must be manually configured to accommodate it, but these procedures limit multicast routing among the most optimal conditions, ensuring that digital resources move effectively and safely to the appropriate parties. However, multicast routing has a wide range of different applications. Here's a look at a few of the most frequent ones, how they work, the many types of multicast travel, and the most popular protocols and instances that prove it's a timeless concept.